- InfoSec Blog
- Risk Analysis: The Cornerstone of Information Security in Every Organization
Risk Analysis: The Cornerstone of Information Security in Every Organization
In today’s cyber world, information security is no longer just the responsibility of the IT department. Cybersecurity concerns every employee and process - from handling customer data to everyday email usage.
To understand and manage the real information security risks in your organization, a thorough information security risk analysis is essential.
What is an Information Security Risk Analysis?
Information security risk analysis is a systematic process aimed at identifying, assessing, and managing risks that may affect an organization’s information, IT systems, and business processes. It is no longer merely a compliance requirement or a formal paperwork exercise. Instead, it is a management tool that helps make informed decisions and allocate resources where information security risks matter most.
Risk analysis should, at a minimum, answer the following questions:
- What is valuable to us? (customer data, contracts, trade secrets, information systems)
- What could happen? (data leaks, cyberattacks, system failures, human error)
- How severe would the consequences be? (financial loss, reputational damage, operational downtime)
How to Conduct an Information Security Risk Analysis
There are multiple methodologies for risk analysis, but the general logic is similar, usually consisting of the following steps:
- Asset identification – tuvastatakse kriitilised infosüsteemid, andmed ja protsessid.
- Threat and vulnerability mapping – analyze what could pose a threat to the assets.
- Risk assessment – evaluate the likelihood of a threat materializing and its potential impact.
- Risk treatment – decide whether to reduce, avoid, transfer (e.g., through insurance), or simply accept the risks.
- Monitoring and updating – risk analysis is not a one-time activity; it is an ongoing process that must be regularly reviewed and updated.
What Makes a Good Information Security Risk Analysis Tool?
ISO/IEC 27001 Eitsify App is designed to make risk management simple, intuitive, and practical. This information security tool provides comprehensive reporting, automatic adaptation, and support throughout the risk management lifecycle - from threat identification to risk treatment. Key Eitsify Risk Management Features:
Asset Management
- Ability to enter, classify, and manage critical assets (information assets, networks, devices, etc.)
- Link assets to owners, threats, and risks
- Predefined lists of typical threats (e.g., fire, water, etc.)
- Add and customize threats according to your organization’s specific needs
Risk Assessment
- Assess risk levels by evaluating likelihood and impact
- Evaluate the cost and effectiveness of mitigation measures
- Visual overview of risk levels and trends
Risk Treatment
- Define risk treatment measures: avoidance, reduction, transfer, or acceptance
- Link risks to relevant measures from the E-ITS benchmark security catalog
- Assign risk owners and implementers, set deadlines, costs, and management decisions regarding treatment acceptance - all in one place, clearly and systematically
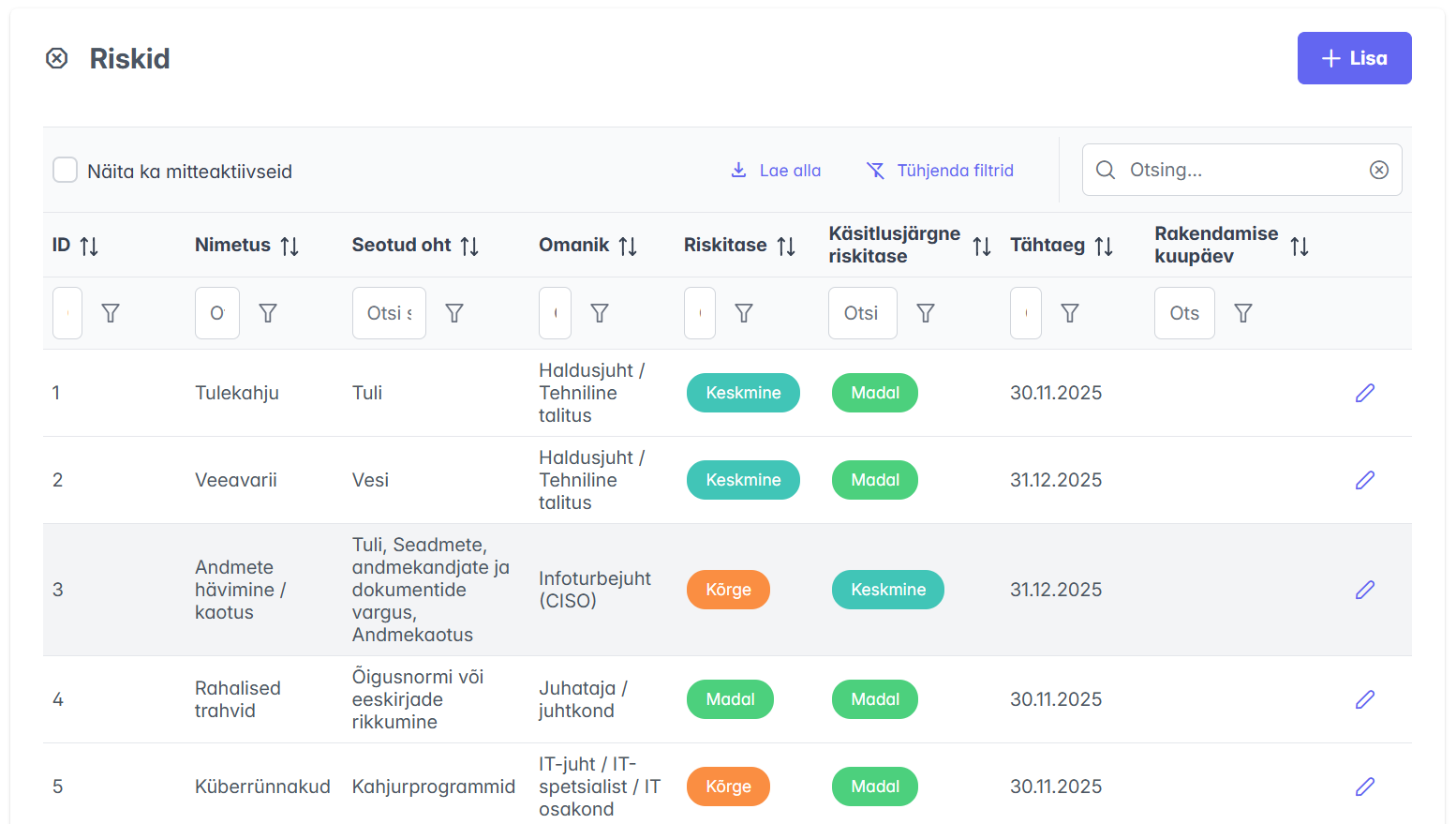
Eitsify Risk Management Module brings all identified information security threats onto a single page. This provides a complete overview of information security risks and their treatment.
Managing risks can sometimes be challenging, but clear visibility and effective risk managementdoesn’t have to be complicated. Our goal is for Eitsify to be the simplest, most intuitive, and most practical information security tool for your organization while implementing ISO 27001.
We work every day to make information security management not burdensome, but genuinely value-creating.
Like Avis .. We try harder .. Every day! 😊


